Somewhere behind your sternum, between your lungs and above your heart, sits an organ most people forget exists. The thymus produces T-cells, the immune system's primary agents for identifying and killing threats. It produces them by the billions. Then it kills almost all of them.
Between 95% and 98% of developing T-cells die in the thymus before they ever enter circulation. They are not defective. They can kill just fine. They failed an identity check.
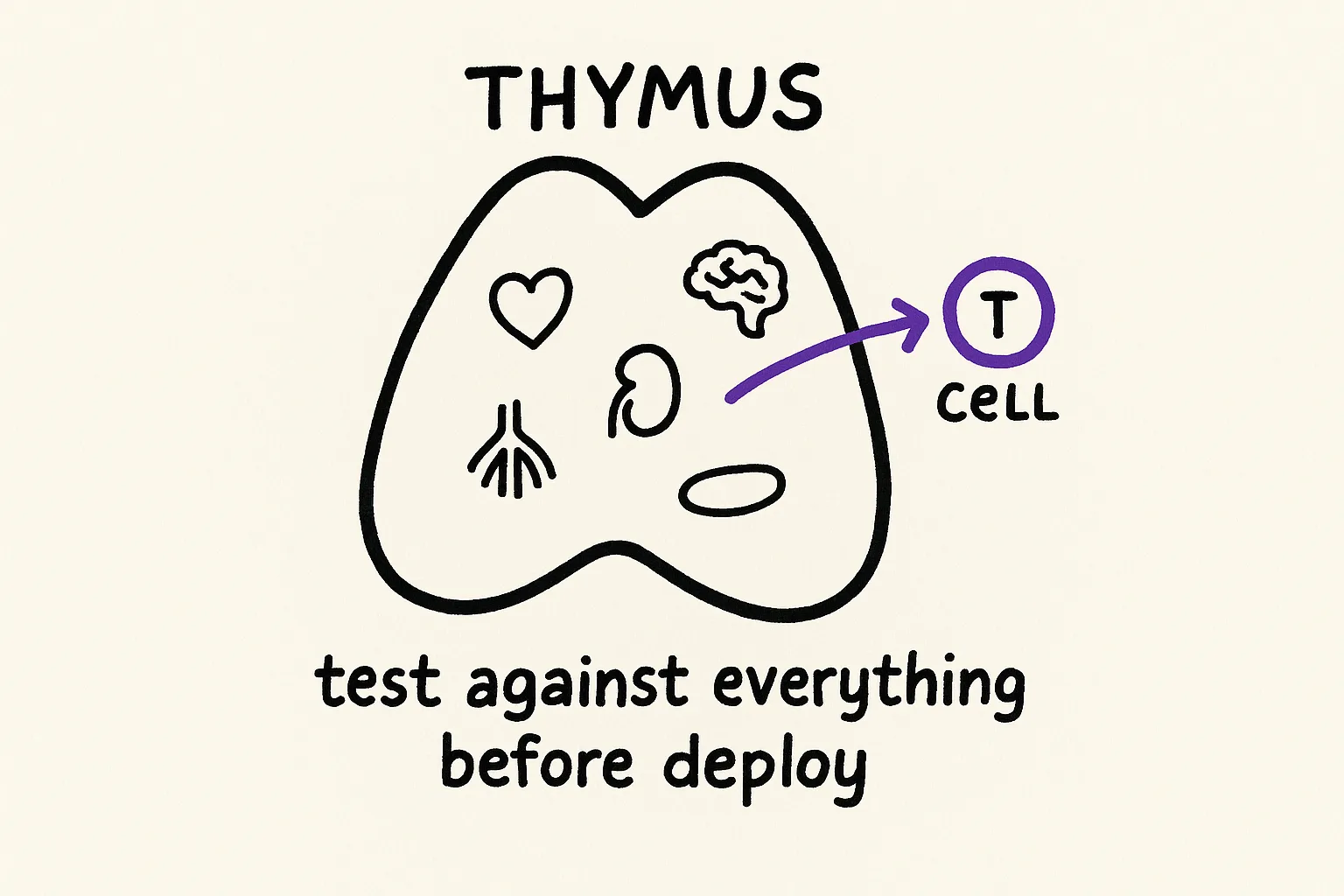
The thymus runs two tests. Positive selection asks: can this cell recognize the body's own molecular identity markers? If not, if the T-cell cannot distinguish self from non-self, it dies of neglect. Roughly 90% are eliminated here. Negative selection asks the opposite: does this cell attack self? Among the survivors, another 50% to 67% are killed because they react too strongly to the body's own tissues. Only cells that pass both, can recognize self and will not attack self, graduate into the bloodstream.
This is not quality assurance. The thymus does not test whether a T-cell can do its job. It tests whether the T-cell knows what it is protecting, what it is not, and where the boundary lies. It pentests identity.
Software teams have spent decades building behavioral testing. Unit tests, integration tests, E2E tests, chaos engineering, fuzz testing. All of it asks one question: does this component do the right thing? Almost none of it asks the question the thymus asks first: does this component know what it is?
QA tests answers. The thymus tests questions.
Traditional testing validates behavior against known expectations. You write a test case because you already know what the correct output should be. Does this function return the right value? Do these two services communicate correctly? Does this user flow complete without error? Every test encodes a known expectation and verifies the system meets it.
This works for the things you think to test. It fails silently for everything else.
Capers Jones's research on defect origins found that roughly 20% of all software defects trace back to requirements and another 25% to design. That is 45% of defects originating before a single line of code is written. The code faithfully implements the intended design. The design itself is wrong. Chris Newcombe and his colleagues at AWS put it directly in their 2015 paper on formal methods: "Some of the more subtle, dangerous bugs turn out to be errors in design; the code faithfully implements the intended design, but the design fails to correctly handle a particular 'rare' scenario."
These are not behavioral bugs. They are identity bugs. The system does exactly what it was told to do, and what it was told to do is incomplete, contradictory, or blind to a scenario nobody thought to specify. No amount of behavioral testing will catch a bug that lives in the specification, because every test you write inherits the same blind spots as the spec it validates.
Identity pentesting operates one layer upstream. Instead of asking "does this component behave correctly?" it asks "is the declaration that defines this component complete, consistent, and honest?" It tests the spec against reality, not the implementation against the spec.
The thymus does not test whether a T-cell can kill an infected cell. It tests whether the T-cell's receptor, its identity declaration, correctly maps the boundary between self and threat. A fundamentally different kind of test. And the immune system runs it first, before any T-cell gets anywhere near a real pathogen.
AIRE built a replica of every organ to run the test
The thymus faces a problem that should sound familiar to anyone who has tried to write comprehensive tests: how do you test a component against conditions it has never encountered?
A T-cell maturing in the thymus has never seen a pancreatic cell. It has never encountered thyroid tissue or liver cells or neurons. But when it graduates into the bloodstream, it will encounter all of them. If it reacts to any of them, the result is autoimmune disease. The immune system attacking the body it is supposed to protect. The thymus needs to test each T-cell against every tissue type in the body, using only the resources available inside the thymus itself.
The solution is a protein called AIRE, the Autoimmune Regulator. AIRE forces thymic epithelial cells to express thousands of proteins that normally appear only in specific distant organs. Insulin from the pancreas. Thyroglobulin from the thyroid. Myelin from nerve sheaths. The thymus builds a molecular catalog of the entire body and uses it to screen every developing T-cell against every tissue the T-cell might later encounter.
When AIRE is defective, the results are catastrophic. People with AIRE mutations develop APECED (autoimmune polyendocrinopathy-candidiasis-ectodermal dystrophy), a syndrome where the immune system attacks multiple organs simultaneously. The T-cells that should have been eliminated were never tested against the tissues they would later encounter. They passed every check the thymus could run. The checks were incomplete.
AIRE turned out to be only part of the story. Single-cell genomics research published between 2022 and 2024 revealed something stranger. Subsets of thymic epithelial cells do not just randomly express peripheral-tissue proteins. They differentiate into what researchers now call mimetic cells, adopting the chromatin landscape, transcription factor usage, and phenotypic features of specific peripheral cell types. Tuft cells, keratinocytes, hepatocytes, neuroendocrine cells, muscle cells, ciliated cells. Each mimetic cell uses the same lineage-defining transcription factors as its real counterpart elsewhere in the body. The thymus is not sampling proteins at random. It is building miniature functional replicas of the body's cell types to screen T-cells against.
Your DNA declaration is the AIRE of your system. It exposes developing components to the full surface area of what they will encounter in production. If the declaration is incomplete, if it catalogs the payment service's identity but not the audit trail's constraints, or the API contract but not the data residency requirements, then components that should fail the identity check will pass it. They will look correct in testing. They will cause autoimmune-equivalent failures in production, the system attacking its own integrity because it was never tested against the full scope of what it needs to coexist with.
A DNA declaration that only covers the happy path is a thymus without AIRE. It will produce components that seem healthy until they encounter the tissue type nobody thought to test against.
Three ways identity verification fails
The immune system's identity checks are not perfect. When they fail, the failure modes look a lot like what happens in software systems that ship components without identity verification.
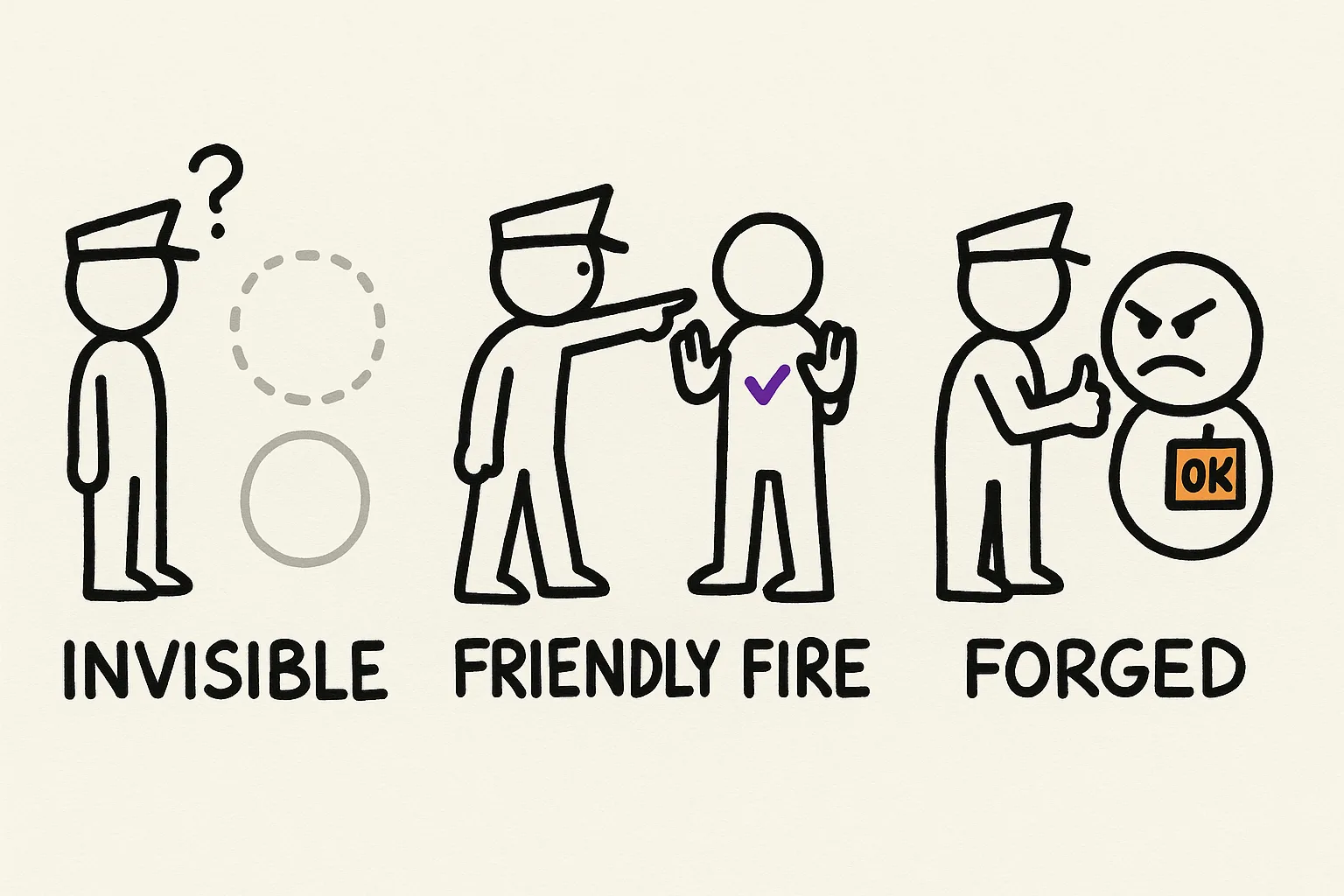
Invisible threats. Cancer cells evade immune detection by stripping their identity markers. MHC class I downregulation has been documented in 40-90% of human tumors, depending on cancer type. MHC-I molecules are the molecular ID badges that every nucleated cell displays on its surface, presenting fragments of internal proteins for T-cell inspection. When a cancer cell loses MHC-I expression, whether through genetic deletion, epigenetic silencing, or loss of the beta-2-microglobulin gene required for surface display, it becomes invisible to the very T-cells designed to destroy it. The threat is real. The identity check cannot see it.
In software, this is the component that strips its own identity to bypass governance. A service that drops its audit trail. An agent that operates without the credentials that would make its actions traceable. A module that removes its DNA declaration and operates outside the identity layer entirely. If your identity verification only works when components voluntarily participate, you have the same vulnerability as an immune system that only catches cancer when the cancer cooperates.
Friendly fire. When AIRE fails or thymic selection is incomplete, T-cells that react to the body's own tissues escape into circulation. The result is autoimmune disease. Rheumatic fever, where antibodies raised against Streptococcal M protein cross-react with cardiac myosin and attack heart valve tissue. Type 1 diabetes, where T-cells destroy insulin-producing beta cells in the pancreas. Multiple sclerosis, where immune cells attack myelin sheaths around nerve fibers.
In software, this is the overly restrictive identity declaration that blocks legitimate components. A DNA layer that declares too-tight boundaries, rejecting valid integrations because the identity rules cannot distinguish a genuine extension from a violation. Teams that encounter this failure mode tend to disable identity checks entirely rather than fix the declaration. That is how you get from autoimmune disease to immunodeficiency.
Forged credentials. Some pathogens survive by disguising their surface molecules to resemble the host's own tissues. The lipooligosaccharides on Campylobacter jejuni structurally mimic human gangliosides, glycolipids that sit on nerve cell membranes. When the immune system generates antibodies against the bacteria, those antibodies cross-react with the gangliosides on peripheral nerves, causing Guillain-Barre syndrome. The pathogen passes the identity check because it forged a credential the immune system accepts as self.
The software equivalent is a dependency that passes your identity checks because it structurally resembles a trusted component. A package that implements the right interfaces, exposes the right API surface, matches the right contracts, but serves a different purpose than what your identity layer expects. The 2022 discovery that Epstein-Barr virus proteins structurally mimic the brain protein GlialCAM, increasing multiple sclerosis risk 32-fold, is a reminder that the most dangerous identity failures are not the obvious ones. They are the ones that look legitimate from every angle your current checks can see.
Cancer cells figured out credential spoofing too
The immune system has a checkpoint mechanism that works like an authorization layer. T-cells that detect a potential threat check for a "stand down" signal before attacking. Healthy tissue expresses PD-L1, which binds to PD-1 on the T-cell surface. The message: I am authorized, do not engage.
Cancer cells exploit this by upregulating PD-L1, displaying the same "authorized" credential that healthy tissue uses, to suppress the T-cells that would otherwise destroy them. The cancer cell is not hiding. It is actively presenting a stolen credential and telling the security system to stand down.
This is why checkpoint inhibitor immunotherapy works. Drugs like pembrolizumab and nivolumab block the PD-1/PD-L1 interaction, preventing cancer cells from flashing the fake credential. The T-cells can then see and attack the tumor. PD-L1-positive tumors respond to checkpoint inhibitors at substantially higher rates than PD-L1-negative tumors, which evade through other mechanisms like MHC-I downregulation.
Two evasion strategies, both targeting identity. One strips the badge so the guard cannot see you. The other flashes a fake badge so the guard waves you through. Some cancers, through downregulation of the transcription factor IRF2, achieve both simultaneously: MHC-I low and PD-L1 high. Invisible, and actively suppressing whatever detection remains.
An identity layer that only checks "does this component have a valid declaration?" is vulnerable to the same spoofing. The check needs to verify not just that the credential exists, but that it is consistent with the component's actual behavior. A service that declares itself a read-only data accessor but makes write calls is the software equivalent of a cancer cell displaying PD-L1. The credential is technically valid. The behavior contradicts it. The gap is where the damage happens.
What identity pentesting actually looks like
Behavioral testing asks: does the system work? Identity pentesting asks: does the system know what it is?
The practice runs five probes against the DNA layer, each targeting a different class of identity failure.
The first is completeness. For every identity claim in the declaration, is there a verifiable counterpart in the implementation? If the DNA declares that the service maintains a complete audit trail, does the audit trail actually capture every state transition? This is the AIRE test. Are you testing your components against the full surface area of what they will encounter, or only the subset you thought to catalog?
Property-based testing offers a concrete mechanism here. Research published in 2025 found that each property-based test discovers roughly 50 times as many mutations as the average unit test, not because it runs more inputs, but because it tests a property (an identity claim about how the system should behave across all inputs) rather than a specific example. 76% of the mutations caught were found within the first 20 inputs. The power comes from testing the right claim, not from testing more cases.
The second is consistency. Do the declarations contradict each other? A service cannot declare P99 latency under 200ms and also declare synchronous calls to three downstream services with their own latency budgets. A component cannot declare itself stateless while maintaining session affinity. Inconsistent declarations are the identity equivalent of an autoimmune trigger, two parts of the system that will inevitably fight each other because their identities are incompatible.
Third, boundary integrity. Can a component do something its declaration says it should not? If the DNA declares that a service does not handle user authentication, can the service actually reach the auth database? If a component's identity excludes reporting functionality, does it have any code paths that generate reports? This is negative selection. Testing whether the component respects its own boundaries, not just whether it fulfills its stated purpose.
Fourth, mimicry resistance. Could a foreign component pass your identity checks? If an external dependency implements the same interface as a trusted internal service, does your identity layer distinguish between them? Could a compromised package declare the same DNA as a legitimate one and operate inside your trust boundary? The immune system solves this with MHC restriction. T-cells only recognize antigens presented by the body's own MHC molecules, not free-floating proteins. Your identity layer needs an equivalent: verification that the declaration is not just structurally correct but originates from a trusted source.
Fifth, the evaporation audit. Are the declarations still current? 2025 research on epigenetic noise in the thymus revealed that thymic epithelial cells deliberately loosen their chromatin packaging, amplifying controlled instability, to enable expression of genes that would otherwise be silenced. When researchers stabilized the chromatin by enhancing p53 activity, the thymus lost its ability to test T-cells against peripheral tissues, and the mice developed multi-organ autoimmune disease. A verification system that becomes too rigid, that locks in its assumptions and stops re-examining them, will miss the threats that evolved after the assumptions were set. DNA declarations written eighteen months ago encode the constraints of a system that existed eighteen months ago. If nobody reviews them, agents will converge toward an outdated target.
The 32-fold risk you are not testing for
In 2022, a longitudinal study of over 10 million US military personnel found that infection with Epstein-Barr virus increased the risk of developing multiple sclerosis 32-fold. No other virus, including the closely related cytomegalovirus, showed increased risk. Serum neurofilament light chain (a biomarker of neural damage) rose only after EBV seroconversion, not before.
The mechanism: EBV nuclear antigen 1 structurally mimics the brain protein GlialCAM. Antibodies generated against the virus cross-react with the brain protein and attack it. The immune system is working correctly. The identity check is working correctly. The identity check was never designed to distinguish between EBNA1 and GlialCAM, because nobody knew they looked the same.
This is the class of failure that identity pentesting surfaces. Not the bugs you have test cases for. The bugs hiding in identity gaps. Places where two things that should be distinct are not distinguished by your current verification. Declarations that are technically correct but structurally incomplete. Boundaries that exist on paper but are not enforced by anything that can measure them.
The 2024 DORA report found that a 25% increase in AI-assisted coding correlated with a 7.2% decrease in delivery stability. Faster code generation without better specification and identity governance produces more output with the same blind spots. More code faithfully implementing a design that fails to handle scenarios nobody specified. The problem is not the code. The problem is upstream.
Monday morning
Start with what you have. A DNA declaration, a CLAUDE.md, a design doc, even a thorough README. Any of these is material to pentest.
The completeness probe is the easiest entry point. For every claim in the declaration, ask: can I verify this automatically? "All API responses under 200ms at P99" is verifiable. "We maintain high reliability" is not. Rewrite every unverifiable claim into something measurable, or acknowledge that it is aspirational rather than architectural.
Consistency requires reading every declaration in your system side by side and looking for conflicts between services that share boundaries. A payment service that declares P99 under 200ms cannot depend synchronously on a fraud detection service that declares P95 under 500ms. If your declarations are individually coherent but collectively contradictory, you have found an autoimmune trigger waiting to fire.
For boundary integrity, pick every "this service does not" clause and verify that the constraint is enforced by something other than good intentions. Can the service reach the resources it claims to exclude? Does the codebase contain functionality that the declaration explicitly scopes out?
Schedule the evaporation audit quarterly. Your immune system continuously re-earns its tolerance by testing against current tissue states, not historical snapshots. Your DNA declarations need the same discipline. Which constraints still hold? Which contracts have drifted? Which boundaries have been crossed without anyone updating the declaration?
The gap between what you test for and what actually breaks is not a gap in your test suite. It is a gap in your identity layer. Test what the component is before you test what it does. The failures that really hurt are never the ones where behavior deviates from the spec. They are the ones where the spec itself was never complete enough to catch what went wrong.
Identity pentesting starts with a declaration specific enough to test against. We are building the tooling that makes DNA declarations verifiable, not just aspirational.
